The blue horizon of the Caribbean is usually the only thing on a Carnival cruise passenger’s mind, a vast, salt-sprayed promise of escape from the humdrum of the daily grind. But behind the scenes, far from the poolside cocktails and the rhythmic thrum of the engine room, a different kind of storm has been brewing—one that doesn’t involve wind or waves, but lines of malicious code snaking through the digital bloodstream of a global titan. The recent breach at Carnival Corporation isn’t just another headline about lost data; it’s a chilling wake-up call that the massive, sprawling supply chains keeping our modern world afloat are held together by digital threads thinner than we ever dared to imagine.
The Hidden Architecture of Our Leisure
When you swipe your “Sign & Sail” card at a cruise ship bar, you’re doing more than ordering a drink; you’re engaging with a gargantuan, interconnected supply chain ecosystem. Carnival, being the world’s largest cruise operator, manages a logistical behemoth that rivals small nations. From the fresh produce sourced in local ports to the sophisticated software managing cabin assignments and guest health records, the company relies on a tapestry of third-party vendors, software providers, and logistics partners. Every one of those touchpoints is a potential door left slightly ajar, waiting for the wrong person to turn the handle.
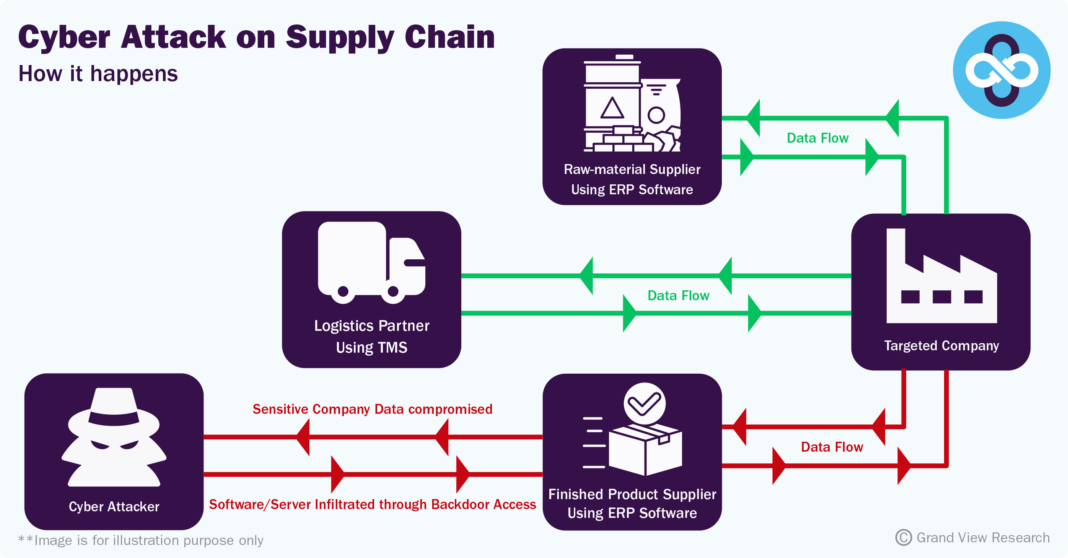
This breach reminds us that we often view corporations as monolithic fortresses, but in reality, they are more like sprawling, porous neighborhoods. When a hacker targets a company like Carnival, they aren’t always trying to break down the front gate. Often, they look for the weakest link in the chain—perhaps a small, third-party logistics firm with lax security protocols or a software update that hasn’t been properly vetted. It’s a sobering realization: your personal information is only as secure as the smallest, least-funded vendor in the massive web of services that keeps your vacation running smoothly.
A Masterclass in Digital Vulnerability
The anatomy of this attack highlights a growing trend in cybersecurity threats that should keep every IT director up at night. We aren’t just looking at a simple phishing attempt or a brute-force entry; we are seeing sophisticated actors exploiting the complexity of modern business. By infiltrating the supply chain, these attackers gain a foothold in trusted environments, moving laterally through systems that were designed for efficiency and connectivity, not for the kind of digital warfare we’re seeing today. It’s a classic case of the very technology meant to streamline our lives becoming the primary vector for our undoing.
For the average traveler, the fallout feels distant, perhaps limited to an email about password resets or a vague notification about “unauthorized access.” But the reality is far more invasive. These vulnerabilities expose the underlying fragility of the systems we trust with our identity, our financial data, and our movements. When these systems falter, it’s not just a technical glitch; it’s a breakdown of the invisible contract of trust between the consumer and the corporation. The Carnival incident serves as a stark reminder that in our hyper-connected age, the “supply chain” isn’t just about moving goods from A to B—it’s about the constant, high-stakes movement of data, and right now, that data is under siege.
As the forensic teams continue to pick through the digital rubble, the questions mounting aren’t just about how this happened, but what happens when the next link in the chain snaps. We’ve become remarkably adept at building systems that can track a head of lettuce from a farm to a galley kitchen in the middle of the Atlantic, yet we seem to be lagging in our ability to protect the very infrastructure that makes that global coordination possible. The industry is currently scrambling to patch these holes, but the question remains: is this a fix for a singular catastrophe, or are we witnessing the inevitable result of a business model that prioritized speed and integration over fundamental cyber-resilience? For more on this topic, see: Apple’s Budget MacBook Just Got .
The Ripple Effect: When Digital Plumbing Fails
We often treat digital infrastructure like the plumbing in our homes: we only notice it when the pipes burst. In the case of a maritime giant like Carnival, the “plumbing” isn’t just about email servers or passenger manifests; it’s about the lifeblood of the vessel itself. Modern cruise ships are essentially floating smart cities, reliant on Operational Technology (OT) to control everything from ballast water systems and propulsion to climate control and food refrigeration. When an external breach occurs, the danger isn’t just the theft of a credit card number—it’s the potential for lateral movement from the business network into the systems that keep the ship operating safely at sea.
The complexity of this integration is staggering. To visualize how these risks are distributed across the industry, we can look at the typical tiers of digital dependency that a major cruise operator must manage:
| Vendor Category | Digital Access Level | Primary Risk Factor |
|---|---|---|
| Maritime Logistics | High (Operational data) | Supply chain disruption |
| Cloud Service Providers | Critical (Data hosting) | Large-scale data exfiltration |
| Onboard Retail/Dining | Moderate (POS systems) | Payment data interception |
| Satellite Communications | High (Connectivity) | Man-in-the-middle attacks |
This tiered structure reveals the vulnerability: the more integrated a vendor is, the more “trust” the corporation must extend. In the cybersecurity world, this is known as the “Zero Trust” challenge. When a third-party software provider has a backdoor into the ship’s manifest system, they effectively have the keys to the kingdom. If that provider’s own security is compromised, the cruise line inherits that failure instantly. It is a domino effect that turns a localized hack in a small office halfway across the world into a massive operational headache in the middle of the Atlantic. For more on this topic, see: What Google’s Nano Banana AI .
Beyond the Firewall: A New Era of Maritime Vigilance
The industry is now at a crossroads. For decades, the maritime sector operated on a philosophy of “security through obscurity”—the idea that ships were so remote and their systems so specialized that hackers wouldn’t bother with them. That era is dead. Today, the International Maritime Organization (IMO) has begun formalizing requirements for cyber risk management, recognizing that a ship’s navigation and safety systems are now as much digital assets as they are mechanical ones. You can find more on their framework for maritime safety at the International Maritime Organization official portal. For more on this topic, see: Tales Of Phantasia Cross Edition .
However, regulation is only the beginning. The real shift must happen in the corporate culture of the supply chain. We need to move away from the “set it and forget it” mentality regarding vendor contracts. True security now requires constant auditing of the digital handshake between a corporation and its partners. It means asking uncomfortable questions: Does this vendor really need admin access to our cloud? Is this data encrypted at rest, or just in transit? Organizations like the National Institute of Standards and Technology (NIST) provide robust frameworks that companies are increasingly adopting to manage these third-party risks, moving away from reactive patches toward a proactive, resilient posture.
The Human Cost of Connectivity
Ultimately, we must remember that behind every line of compromised code is a person. It’s the passenger who just wanted a week of relaxation, the crew member whose payroll data is now floating on a dark web forum, and the IT professional working through the night to rebuild a fractured system. This breach is a reminder that our digital lives are inextricably linked to the physical world. We have traded the isolation of the high seas for the convenience of constant connectivity, and with that trade comes a new set of responsibilities.
As we move forward, the resilience of our global supply chains will depend on our ability to prioritize security over sheer convenience. The “Carnival lesson” is a hard one, but it is necessary. It teaches us that in our hyper-connected age, the strength of the whole is defined by the integrity of the smallest, most obscure link in the chain. We aren’t just protecting databases; we are protecting the public trust that allows our modern, globalized world to function. It is time for corporations to stop viewing cybersecurity as a line item on an IT budget and start viewing it as a fundamental pillar of their social contract with the people they serve. For those interested in the broader technical standards governing these systems, the International Organization for Standardization (ISO) provides detailed guidelines on information security management that are becoming the gold standard for global enterprises.